Below is a list of the most common customer questions. If you can’t find an answer to your question, please don’t hesitate to reach out to us.
What is cybersecurity assessment?
Cybersecurity assessment is the process of identifying, assessing, and managing risks related to the security of an organization’s information, systems, and networks. It involves an in-depth analysis of an organization’s existing security posture, identifying any vulnerabilities, threats, and risks, and providing recommendations for improvement. The assessment typically includes a review of the organization’s security policies and procedures, network security architecture, applications, and security systems. Cybersecurity assessments can be conducted internally or by a third-party organization.
Who is required to file cybersecurity assessment?
Cybersecurity assessments are typically required for any organization that collects, stores, or processes sensitive data. This includes any business that operates online, stores customer information, or handles payment information. It also includes any organization that handles government data, such as healthcare providers, universities, and financial institutions.
How to fill out cybersecurity assessment?
Filling out a cybersecurity assessment involves gathering information and evaluating your organization's current cybersecurity posture. Here are the general steps to follow:
1. Understand the purpose: Familiarize yourself with the purpose and scope of the cybersecurity assessment. Determine which areas or aspects of cybersecurity the assessment is targeting.
2. Gather information: Collect all relevant information about your organization's network infrastructure, IT systems, applications, data, policies, and procedures. This may include network diagrams, system inventories, asset lists, access controls, incident response plans, and compliance documentation.
3. Define assessment criteria: Understand the assessment criteria set out by the assessment form or questionnaire. It may involve rating your organization's cybersecurity practices, identifying vulnerabilities, or complying with specific regulatory requirements.
4. Review and evaluate: Go through the assessment questions or sections and evaluate your organization's current practices against each criteria. This may involve identifying gaps in security controls, areas of risks, or non-compliance.
5. Provide relevant evidence: Collect and provide any relevant evidence or documentation to support your assessment answers. This could include security policies, logs, vulnerability assessment reports, penetration testing results, or third-party audit reports.
6. Prioritize and remediate: Identify the most critical weaknesses or gaps in your cybersecurity posture and prioritize them based on their potential impact. Develop a plan to remediate or mitigate identified vulnerabilities or risks.
7. Review and validate: Reread and validate your assessment responses, ensuring that they accurately reflect your organization's cybersecurity practices. Make sure that all evidence and documentation provided are accurate and up-to-date.
8. Submit assessment: Submit your completed cybersecurity assessment to the designated party or organization responsible for the assessment. Follow any specific submission procedures or formats required.
9. Follow up and track progress: Once the assessment is submitted, follow up with the assessment entity if required. Keep track of any recommendations, action items, or remediation plans resulting from the assessment and ensure progress is made.
Remember to adapt these steps to the specific cybersecurity assessment form or questionnaire you are filling out, as requirements may vary.
What is the purpose of cybersecurity assessment?
The purpose of a cybersecurity assessment is to evaluate the effectiveness of an organization's cybersecurity measures and identify vulnerabilities, risks, and weaknesses within its systems, networks, and infrastructure. It aims to assess the organization's security posture, identify potential threats, and determine the appropriate measures to mitigate those risks. A cybersecurity assessment helps organizations understand their current security capabilities, prioritize and allocate resources efficiently, and establish a roadmap for improving their overall cybersecurity posture to safeguard against cyber threats, attacks, data breaches, and unauthorized access.
What information must be reported on cybersecurity assessment?
The specific information that must be reported on a cybersecurity assessment may vary depending on the organization and the regulatory requirements they are subject to. However, some common elements that are typically included in cybersecurity assessment reports are:
1. Executive Summary: Provides a high-level overview of the assessment, its objectives, key findings, and recommendations.
2. Scope: Defines the boundaries and limitations of the assessment, outlining the systems, networks, or processes that were evaluated.
3. Methodology: Describes the approach and tools used for conducting the assessment, including any penetration testing, vulnerability scanning, or other techniques employed.
4. Threat Landscape: Analyzes the current cyber threat landscape, including emerging threats and recent attacks relevant to the organization.
5. Risk Assessment: Identifies and assesses potential vulnerabilities and risks to the organization's systems, networks, or data.
6. Findings: Presents the findings of the assessment, including any vulnerabilities or weaknesses identified in the organization's cybersecurity posture.
7. Recommendations: Provides actionable recommendations on how to address the identified vulnerabilities or weaknesses, including technical controls or process improvements.
8. Remediation Plan: Outlines a detailed plan for addressing the identified vulnerabilities and weaknesses with timelines, responsible parties, and prioritization.
9. Compliance: Evaluates the organization's compliance with relevant cybersecurity regulations or standards and highlights any areas of non-compliance.
10. Summary and Conclusion: Provides a concise summary of the assessment, reiterating key findings, recommendations, and the overall effectiveness of the organization's cybersecurity measures.
It's important to note that the specific requirements for reporting cybersecurity assessments may differ based on industry-specific standards or legal regulations that an organization must adhere to, such as the General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), or Payment Card Industry Data Security Standard (PCI DSS).
What is the penalty for the late filing of cybersecurity assessment?
The penalty for the late filing of a cybersecurity assessment can vary depending on the specific laws and regulations of the jurisdiction in question. Organizations and individuals that fail to file cybersecurity assessments on time may face financial penalties, such as fines or monetary sanctions. These penalties are typically imposed to encourage compliance with cybersecurity requirements and to deter negligent or non-compliant behavior. It is important to consult the relevant legislation or regulatory body to determine the specific penalties that may be imposed for late filing of a cybersecurity assessment.
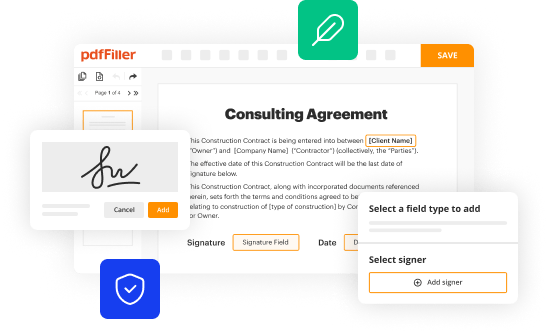
How can I edit cybersecurity assessment on a smartphone?
The pdfFiller apps for iOS and Android smartphones are available in the Apple Store and Google Play Store. You may also get the program at https://edit-pdf-ios-android.pdffiller.com/. Open the web app, sign in, and start editing ffiec cybersecurity assessment tool form.
Can I edit cybersecurity assessment tool on an iOS device?
Create, modify, and share ffiec cybersecurity assessment tool download using the pdfFiller iOS app. Easy to install from the Apple Store. You may sign up for a free trial and then purchase a membership.
How do I complete cybersecurity assessment template on an Android device?
On an Android device, use the pdfFiller mobile app to finish your ffiec assessment form. The program allows you to execute all necessary document management operations, such as adding, editing, and removing text, signing, annotating, and more. You only need a smartphone and an internet connection.