Last updated on May 20, 2026

FFIEC Cybersecurity Assessment Tool 2015-2026 free printable template
pdfFiller is not affiliated with any government organization
Why pdfFiller is the best tool for your documents and forms
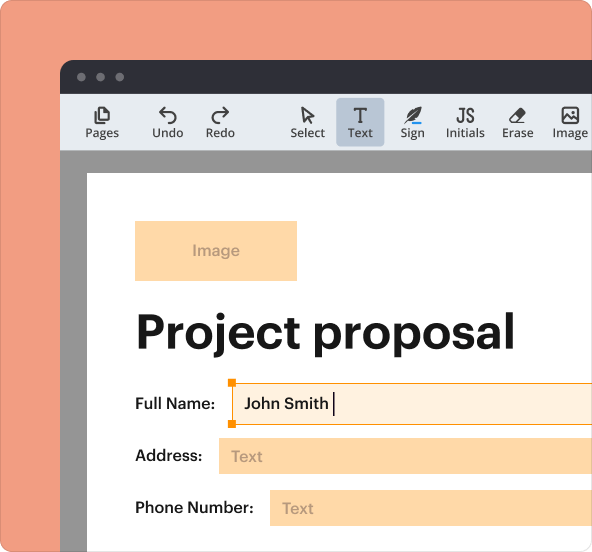
End-to-end document management
From editing and signing to collaboration and tracking, pdfFiller has everything you need to get your documents done quickly and efficiently.
Accessible from anywhere
pdfFiller is fully cloud-based. This means you can edit, sign, and share documents from anywhere using your computer, smartphone, or tablet.
Secure and compliant
pdfFiller lets you securely manage documents following global laws like ESIGN, CCPA, and GDPR. It's also HIPAA and SOC 2 compliant.

What is FFIEC Cybersecurity Assessment Tool
The FFIEC Cybersecurity Assessment Tool Overview is a guidance document used by financial institutions to identify cybersecurity risks and assess preparedness.
pdfFiller scores top ratings on review platforms




Who needs FFIEC Cybersecurity Assessment Tool?
Explore how professionals across industries use pdfFiller.
Comprehensive Guide to FFIEC Cybersecurity Assessment Tool
Understanding the FFIEC Cybersecurity Assessment Tool Overview
The FFIEC Cybersecurity Assessment Tool serves as a vital resource aimed at helping financial institutions evaluate their cybersecurity posture. Its primary purpose is to assist organizations in identifying cybersecurity vulnerabilities and ensuring awareness of potential risks. By conducting a cybersecurity risk assessment, financial institutions can better understand their vulnerability landscape and the importance of proactive measures.
This tool provides a framework for assessing cybersecurity maturity, tailoring its approach according to the institution's inherent risk profile. Its structured methodology aligns with industry standards, ensuring institutions can effectively gauge their readiness against cybersecurity threats.
Purpose and Benefits of Using the FFIEC Cybersecurity Assessment Tool
Utilizing the FFIEC Cybersecurity Assessment Tool offers numerous advantages for financial institutions. Primarily, it empowers organizations to uncover and address potential cybersecurity weaknesses. Enhanced cybersecurity preparedness and oversight are crucial for managing risks effectively, fostering a culture of vigilance within organizations.
Moreover, chief executive officers and boards of directors will find this tool invaluable in their roles. It enables them to take informed measures and apply a management framework that addresses cybersecurity risks comprehensively. This strategic oversight is essential for safeguarding organizational assets.
Key Features of the FFIEC Cybersecurity Assessment Tool
The assessment tool is composed of several key features designed to streamline the evaluation process. At the core, it encompasses components such as risk profiling and descriptions of maturity levels that institutions can achieve. This narrative-driven format avoids formal fillable fields, allowing for richer informational content and insights.
An emphasis on alignment with FFIEC cybersecurity guidelines further reinforces its reliability. These best practices ensure organizations follow a structured approach when assessing their cybersecurity capabilities.
Who Should Use the FFIEC Cybersecurity Assessment Tool
The FFIEC Cybersecurity Assessment Tool is structured to benefit diverse roles within financial institutions. Management and board members are the primary users who can leverage the tool for strategic decision-making. It is especially critical for smaller institutions that may not have comprehensive cybersecurity resources.
Furthermore, compliance officers and risk managers will find significant relevance in utilizing this assessment tool. By implementing its recommendations, they can enhance their oversight and compliance efforts effectively.
How to Access and Utilize the FFIEC Cybersecurity Assessment Tool
To access the FFIEC Cybersecurity Assessment Tool, organizations can visit the FFIEC website, where downloadable resources are available. Once obtained, institutions should follow specific steps to review and utilize the tool within their operational frameworks.
-
Begin by assessing the organization’s current cybersecurity posture.
-
Implement the assessment findings into existing risk management strategies.
-
Regularly re-evaluate the cybersecurity measures to adapt to evolving risks.
Adhering to best practices in assessment will facilitate efficient utilization and enhance overall cybersecurity posture.
Enhancing Cybersecurity Management with the FFIEC Tool
The integration of the FFIEC Cybersecurity Assessment Tool findings into an institution’s overarching risk management strategy is essential for effective cybersecurity management. Institutions should prioritize creating actionable plans based on these assessment results. This strategic approach involves defining clear steps to mitigate identified risks and strengthen defenses.
Continuous reassessment is also necessary, as the cybersecurity landscape is ever-evolving. Institutions must engage in regular reviews of their measures to foster ongoing improvement and responsiveness to new threats.
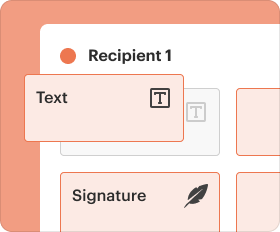
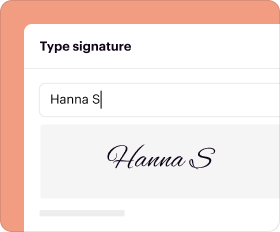
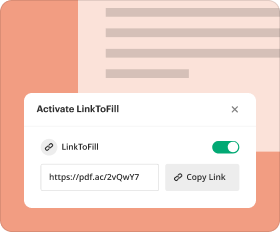
The Role of pdfFiller in Completing Cybersecurity Documentation
pdfFiller plays an important role in securely managing documentation related to cybersecurity assessments. It offers advanced capabilities such as editing, sharing, and eSigning necessary documents, ensuring that the information remains secure throughout its lifecycle.
Notably, pdfFiller employs 256-bit encryption and maintains compliance with regulations such as HIPAA and GDPR, safeguarding sensitive data. Users are encouraged to utilize pdfFiller’s document management platform for seamless handling of all associated documentation.
Maximizing Your Cybersecurity Preparedness Journey with the FFIEC Tool
Regularly assessing cybersecurity risks is a cornerstone of effective governance. By utilizing the FFIEC Cybersecurity Assessment Tool, organizations can take substantial steps towards enhancing their cybersecurity preparedness. Engaging with these tools ensures that institutions remain vigilant and proactive in identifying potential vulnerabilities.
Leveraging pdfFiller can also streamline the documentation process, allowing institutions to focus more on evaluating and strengthening their cybersecurity posture. Early and consistent engagement with the FFIEC resources will facilitate a robust approach to managing cybersecurity risks.
How to fill out the FFIEC Cybersecurity Assessment Tool
-
1.Access the FFIEC Cybersecurity Assessment Tool Overview on pdfFiller by searching for the document directly in the platform's search bar.
-
2.Open the document to view its content. Note that this tool is primarily informational and does not include fillable sections.
-
3.Before using the document, gather necessary resources related to your institution's cybersecurity measures and risk profile.
-
4.Review the tool's framework to understand how it measures cybersecurity maturity and aligns with inherent risk profiles.
-
5.As you navigate through the document, take notes on important points that apply to your institution's circumstances.
-
6.Consult with your team to discuss findings and how they reflect your current cybersecurity standing.
-
7.Finalize your overview by compiling gathered information and insights into a summary report for your records.
-
8.To save or download this guidance for future reference, use the save options in pdfFiller and select the format that best suits your needs, such as PDF.
Who should use the FFIEC Cybersecurity Assessment Tool Overview?
The FFIEC Cybersecurity Assessment Tool Overview is essential for chief executive officers, boards of directors, and cybersecurity risk management professionals in financial institutions.
Is this document a fillable form?
No, the FFIEC Cybersecurity Assessment Tool Overview is not a fillable form. It is an informational document designed to guide institutions in assessing cybersecurity risks.
What is the primary purpose of this tool?
The primary purpose of the FFIEC Cybersecurity Assessment Tool Overview is to assist financial institutions in identifying cybersecurity risks and evaluating their preparedness.
Are there any supporting documents required?
While there are no specific supporting documents required for accessing this overview, it is beneficial to gather existing cybersecurity reports and assessments for a comprehensive analysis.
What common mistakes should be avoided while using this tool?
Common mistakes include misunderstanding the framework, failing to engage relevant stakeholders in discussions, and not using current cybersecurity data for assessments.
How often should cybersecurity assessments be conducted?
Financial institutions should conduct cybersecurity assessments regularly, ideally annually or whenever significant changes in systems or risks occur.
Can I download the FFIEC Cybersecurity Assessment Tool Overview?
Yes, you can save and download the FFIEC Cybersecurity Assessment Tool Overview from pdfFiller in multiple formats, including PDF.
Related Catalogs
If you believe that this page should be taken down, please follow our DMCA take down process
here
.
This form may include fields for payment information. Data entered in these fields is not covered by PCI DSS compliance.